The new INFIMA is here
Run security awareness — and human risk — across every client you manage
INFIMA just relaunched: per-user risk scoring, framework compliance, and dark web monitoring — on the automated, white-labeled, PSA-integrated platform that already protects thousands of clients.
Trusted across thousands of clients
The platform MSPs don’t have to think about
- 18+
- Compliance frameworks supported
- 2.17
- Support tickets per 100 clients
- 99.9%
- Uptime
- 600K+
- False clicks prevented YTD
New in the relaunch
Three new ways to manage risk across your whole book of business
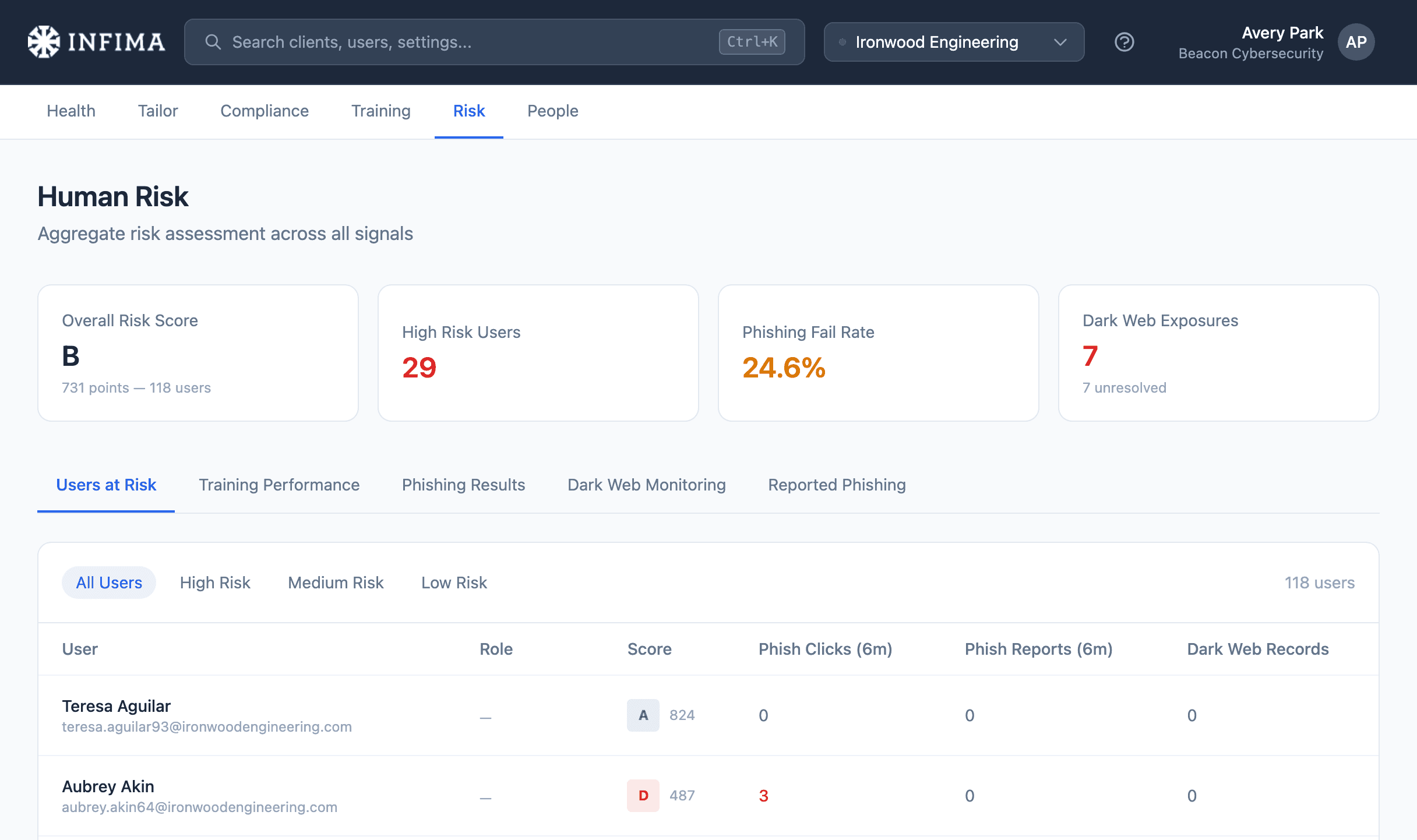
Human Risk ManagementPer-user risk scoring rolled up across every client you manage — see where your exposure really is, from one place.
Compliance & FrameworksAssign one of 18+ frameworks and the audit-ready evidence builds itself — across every client.
Dark Web MonitoringCatch breached credentials the moment they surface — and the user is walked through the fix, so it never becomes a ticket.
Loved by MSPs
The partners who run it say it best
“The time our team spends managing INFIMA is close to zero… it’s set it, forget it.”
“INFIMA’s been so trouble-free that I don’t even know if we’ve ever gone to support… it just does what we need it to do.”
“INFIMA is priced right so we can still make a margin on it, without having to worry about it too much. The integration with 365 makes my life super simple.”
“INFIMA is easy to use, easy to manage, and I don’t even have to think about it… it just works. That’s the best part.”
“We had an issue and I emailed Zach. Within 20 minutes everything was resolved. I like their responsiveness.”
“Automation is key to us being able to do so much with very little. “Set it, forget it” is absolutely something we want for Security Awareness Training — INFIMA delivers that automation.”
See the new INFIMA across your whole book of business.
Book a walkthrough and we’ll show you human risk, compliance, and dark web monitoring the way you’ll actually use them — across every client, from one screen. Or watch the tour first.
Already a partner? Visit the knowledge base