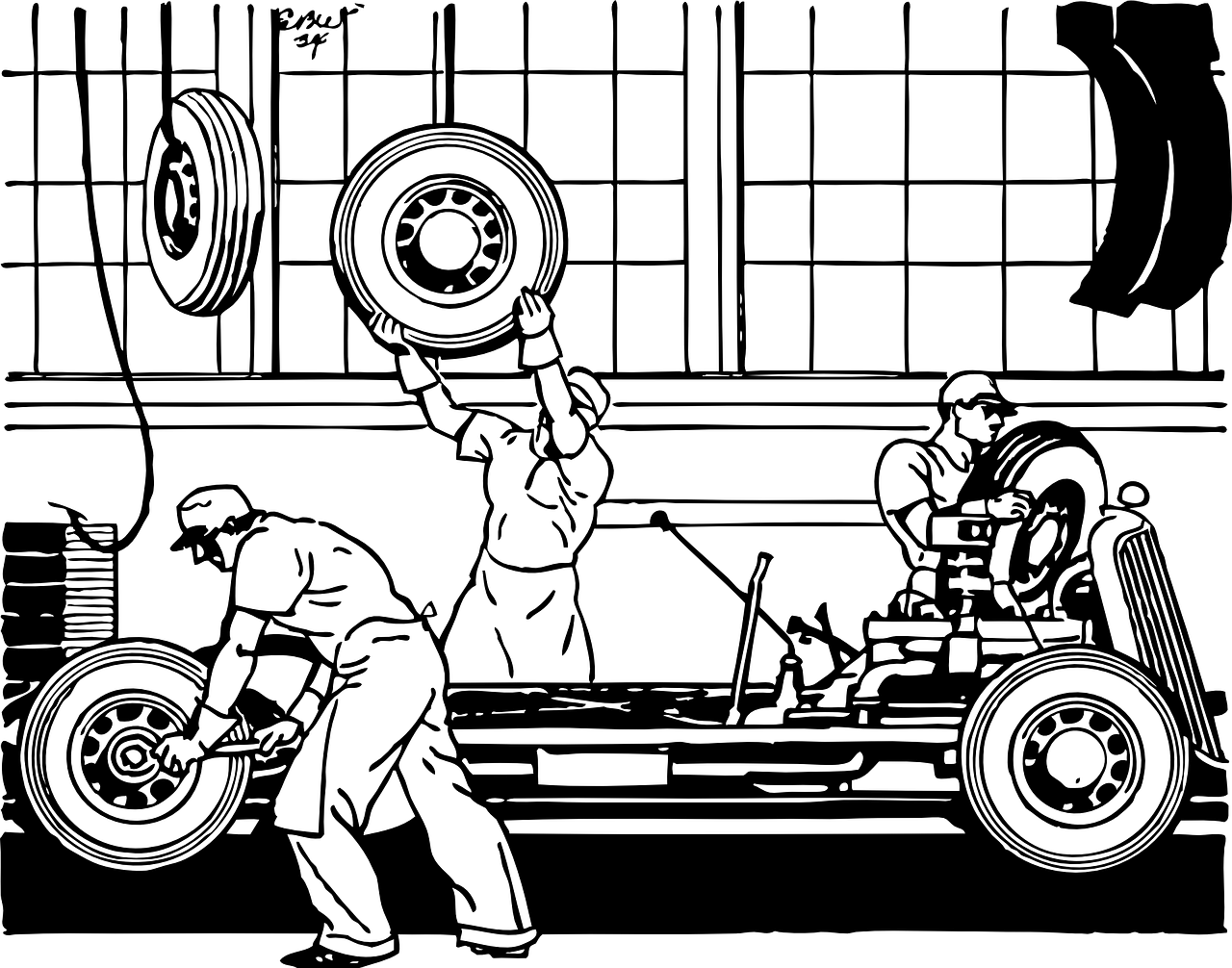
Manufacturing
Pay Up! Or Watch Out For Facebook Ads??
An infamous Ransomware team adds a new media strategy to its hacks.

What Do Canon, Jack Daniels and Carnival Cruises Have In Common?
You may patronize each of these companies on vacation, and now hackers are taking a lot of that money for themselves.

Did Garmin Pay Evil Corp?
Yes, Evil Corp. The hacker group crippled Garmin's systems and happily accepted the company's ransom money.

Chipmaker Exposed in Maze Attack
Maze has struck again. This time stealing sensitive data from a computer chipmaker.
Attack Shuts Order Processing for Philly Manufacturer
alphabroder is North America's largest supplier to the promotional products industry. The Philadelphia-based company was hit with a vicious strain of malware, known as SODINOKIBI. While it appears no sensitive data was lost, the company experienced revenue loss from the attack. “It’s temporarily disabled us from an order processing
Auto Plants Halted After Supplier Breach
At least two Indiana automotive plants were forced to stop work after a successful cyber attack on a key supplier. “The FBI is aware of a ransomware attack and the significant impact that the attack has had on certain companies in the state of Indiana."After receiving word of the
What does an attack on a manufacturing company look like?
Cyber criminals have figured out the value in targeting manufacturers. Using social engineering practices, these attackers exploit the imbedded trust within your organization and amongst your partners, vendors and clients. Once inside your organization, they can patiently plan subsequent moves to extract maximum value. To take these attacks from the
There’s increased scrutiny on cyber security for manufacturers. Why?
In late 2018, major media reports emerged with news that China had inserted a tiny chip into the semiconductor supply chain of 30 US companies, including Apple and Amazon. The brilliance of this attack reveals a critical motivation for hackers targeting manufacturers - by infecting the supply chain of a




